Who am I?
My name is Alex McGeorge and I break into things for a living with Immunity, Inc.
What kinds of things?
- Websites and applications
- Networks
- Other people's software
- Other people (social engineering)
- Physical places
I also teach some of these things to others and occasionally I put on a suit and talk into a camera
Why should you care?
You may value your privacy or be worried that someone is actively trying to snoop on you
Some of the topics we cover in this talk will help you make their job more difficult
A disclaimer
I am not an employee of: Facebook, Google, FetLife, Recon, DropBox, Microsoft, etc.
I can not comment on what they actually do with your data only what is possible
Who is this class for?
- Non IT professionals
- We will also cover only personal privacy and security
A note on choosing your enemies
Nothing I say here will prepare you for a nation state level adversary

Allow me to save you some time: if the NSA is your enemy, you're fucked
What does a site know about you?
Lets use FetLife as an example:
|
|
Does this make FetLife evil?
Not really, any social networking site or forum will have similar information

About Face Recognition and Comparisson
Does that actually work?
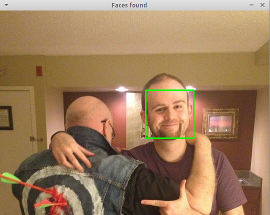 FetLife profile photo |
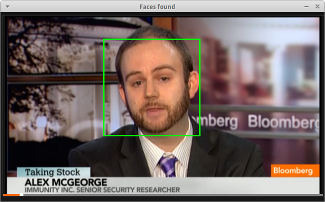 Talking head photo |
It took me about 15m to write up a program to do fairly accurate face detection with freely available libraries
Problems
Q: How do I hide my username/password/email address?
- Make your username and password unique to each site you're on
- This is also useful in that if your password on one site is compromised it can't be used against you on others
- Having a separate email for each site can become impractical but you can have kinky and vanilla addresses

Problems
Q: Can I hide who I'm friends with and who I've conversed with?
- Not really as this is a core functionality of the site
- You could have multiple profiles if you wanted but again that would be hard to manage
- You would have to disguise everything else IP, Browser, etc. to keep the illusion

Problems
Q: Can I hide what I've said?
- Yes! You could use PGP to encrypt your messages
- In our example of FetLife the messaging portion would be cumbersome for this, so instead switch communications channels then encrypt!

Problems
Q: Can I hide my browser and OS?
- Yes! There are many plugins that do this and even native support in some browsers
- Beware though, this problem is more tricky than it sounds

Problems
Q: What about sanitizing my photos?
- If your face is in it, completely remove your face. Don't get cute with a blur, it's possible to undo.
- Reverse image searching is totally viable. Which means, if you have an unsanitized picture on your flickr but use the same picture only sanitized on FetLife, someone can use the sanitized image itself to find the original.
- Most image files contain space for so called EXIF metadata which your phone can use to helpfuly include GPS coordinants and other interesting information
|
File name : dsc_0790.jpg File size : 4654488 bytes File date : 2008:07:16 09:45:20 |
Camera make : NIKON CORPORATION Camera model : NIKON D200 Date/Time : 2007:06:23 22:00:14 |
Resolution : 3880 x 2608 Exposure bias: 1.00 Whitebalance : Auto |
|
Exposure : aperture priority (semi-auto) GPS Latitude : 41.40338 GPS Longitude: 2.17403 |
DateCreated : 20070623 Time Created : 220014 Record vers. : 4 |
EXIF continued
Q: Ok so how do I remove it?
Here are some: Windows Options, Mac Options, and Linux Instructions.
Note: I have only tried the Linux methods

Problems
Q: What about my IP?
- This is an example of an IP: 149.101.1.3
- When someone knows your IP
- They can determine which organization owns that IP (via whois)
- If there is a host name associated with the IP (via reverse DNS)
- What the approximate geographic location of the IP is (via GeoIP)
- The legal system is starting to accept that an IP is not an identity
- Which brings us to...

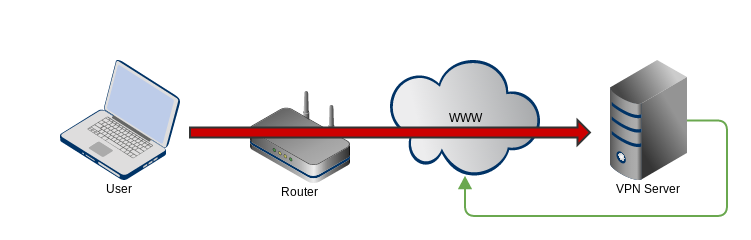
Virtual Private Networks!
Virtual Private Networks (VPNs) allow for two computers to have a private conversation (via encryption) that if intercepted would not be able to be decrypted
This may sound a lot like SSL (the s in https) and it is!
The difference is that with a VPN you send all your traffic through the connection

Problems
Q: This sounds great but are there downsides?
What about Tor?
- Tor is a great technology
- How it works is complicated. But the Reader's Digest version is this:
- You establish an encrypted connection to an entry node on the Tor network
- You then connect through to other servers within the Tor network through a random path you determine
- This network is special in that any one server on the network can only ever know the server that connected to it and the server it will connect to next
- This means that compromising any one server on the network won't let you de-anonymize someone
- VICTORY IS OURS!

Problems
There are a few problems
- Some unsavory types use Tor
- We know Tor users are actively targeted by governments
- Did I also mention that Tor is an invention of the US Navy?

Home Wireless Routers
Let's talk about stopping people from snooping on you via your router
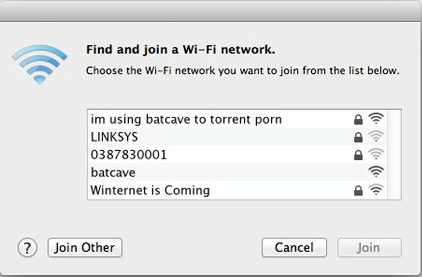
Basic Security Settings
Things that work:
- On use WPA2 with a pre-shared key
- Diable WEP and WPS completely
Things that don't:
- Using a "hidden" SSID
- If clients are actively connected to the wireless network we can see the AP they are connected to
- Filtering based on MAC address
- If clients are actively connected to the AP, we can switch our MAC to theirs and de-auth them
Other good habits
- Change the default admin password for the router's management interface
- Check for firmware updates to the router
- Realize that if the connection that feeds your router is only rated at X, having a wireless router capable of X*10 throughput will actually not speed up your internet experience.
- It will allow you to share files/media between hosts on your home network quicker
What files? Maybe high quality digital scans of a certain manga you happen to enjoy
For example:
Can I use my friend's wireless?
Sure! But a few things to realize
- Any time you give someone a key to your WiFi they can see all the traffic until you change it (if they are within range of the router's wireless signal)
- Sending your traffic through a malicious router gives the router operator an incredible opportunity for villainy
Allow me to tell you about a WiFi network I used to run...
VPNs are a good way to mitigate this risk, get in the habit of using them away from home
What about phones?
Not surprisingly there's a lot to say
Common Questions
Q: Can someone other than law enforcement intercept my cell phone calls?
Yes, the gear to do this has gotten cheaper but is still a few thousand dollars investment
A safe assumption is: it can be done and will only become cheaper to do

Common Questions
Q: What is the most secure phone?
It very much depends on who your enemy is
| Level of Concern | Potential Solution |
| I'm just concerned about malware | Pick whatever phone works for you, keep it up to date, don't download a bunch of apps |
| I have a nosy spouse/partner/parent | Buy a prepaid phone with cash that is 'lockable' | I saw The Wire and that looks cool | Have someone else buy a prepaid phone and dispose of it weekly, leave it off when not in direct use |
| I want to join ISIS | Good luck with that |
Common Questions
Q: If my spouse/partner/parent has physical access to my phone..
Yes, many more things become possible such as
- Retrieving "deleted" texts, emails, photos
- Installing software to covertly send and copy all of the above
- Installing software that tracks your location via GPS etc
- Remotely turning on the phone's microphone/camera

Common Questions
Q: What about Skype and other altnernatives
- Disclaimer: I only know a little bit about Skype
- Intercepting Skype traffic of someone using the same network as you is easy
- Extracting anything meaningful out of the data is very hard (though there is interesting research)
- Verdict: Probably ok unless you are a priority intelligence target

Miscellaneous
Various bits and bobs that I think are relevant to online privacy
Password Managers
- Don't let your browsers save passwords on your behalf to autofill them for convienance
- Don't subscribe to an online service which will "save all your passwords for you"
- For a reasonable discussion of good password managers: see this paper
- I use Password Safe

Full Disk Encryption
FDE encrypts the entire contents of a disk drive such that if anyone steals it they will not be able to retrieve any of the data on it unless they have the password
- Windows BitLocker (Free)
- OSX File Vault (Free)
- As usual there are various options for Linux (also Free)
E-Mail and file based encryption
- PGP (or GPG in this case) is the standard, it even comes for Windows
- I use Thunderbird and Enigmail for e-mail based PGP
- Soon Google will have PGP by default for gmail and Chrome, Yahoo is working on something similar
I want to donate/dispose of an old computer
- Simple solution: remove the hard drive before you donate it, they will always accept it
- To completely wipe a drive use: DBAN
- If you are really paranoid, wipe it then take a hammer to it

Someone leaked my personal info!
- Usernames? Passwords? Change any and all
- Real name, DOB, address? Alert your bank for fraud
- SSN? Account numbers? Alert your bank and the police
- Realize that once information is on the internet and has been seen by many, it is very difficult to get it off
- Contact the site owner and see if they will voluntarily remove the content

I'll get a lawyer!
Do get a lawyer! There are situations they can help you resolve
They can also (hopefully) help you avoid looking like a giant idiot if you have no case
I caught the malware!
- Most malware seeks to turn your computer into a commodity
- Banking details, online accounts to things like Amazon or Steam..
- Your sexy pictures and emails are typically not a commodity
- If someone targets you specifically (which is uncommon) then worry about sexy picture leaks. For example: